A screenshot of a social media analysis platform suspected to be used internally by the Chinese Communist Party’s public security system has recently been circulating online. The screenshot shows that the system integrates account behaviors, device and identity information, and conducts structured modeling on users. The authenticity of the related system has not been independently verified, but the presented technical approach aligns with the direction of strengthening internet control by the CCP in recent years.
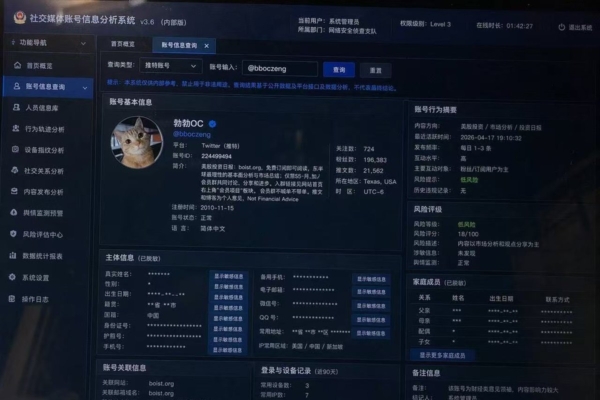
The leaked screenshot of the system is labeled as “Social Media Account Information Analysis System v3.6 (Internal Version)”. The interface displays terms like “Network Security Investigation Squad” and “Permission Level 3,” and features modules for account retrieval, behavior analysis, and risk assessment. The system not only presents account avatars, IDs, number of followers, and posting frequency but also records IP locations, login devices, and browsing histories, capturing users’ actions to form traceable patterns.
Within this interface, sections like “Subject Information” and “Family Members” involve phone numbers, emails, and familial relationships, extending account data to real-life identities and establishing cross-connections through relationship information. By consolidating account behaviors, device information, and real identities, individuals become identifiable and traceable entities within the system.
A mainland Chinese internet engineer, Mr. Mou, remarked during an interview with The Epoch Times that upon seeing the widely circulated image, his initial reaction was that it looked like a photo taken of a monitor with screen reflections. Regardless of the authenticity of the image, the underlying direction it signifies is clear – bridging internet identities with real-world identities. He mentioned encountering a similar system in a company before, one that could connect to home videos. Once operational, such a system could monitor the activities of users on overseas social media platforms at any time.
Mr. Mou emphasized that the focus of such systems lies not in individual pieces of information but in capturing users’ long-term behaviors to form patterns, especially in tracking overseas social media accounts continually.
The screenshot reveals that the system assigns “risk levels” and “risk scores” to accounts, along with behavior tags to categorize user speeches and interactions.
Mr. Mou commented further, stating, “If a mechanism like this exists, it means that when netizens access overseas platforms through circumvention tools, their comments and posted videos will be continually recorded, tracked by this system, and transformed into quantifiable indicators. Through calculations from the model, your actions can be reconstructed, leading to identification. This is no longer mere information monitoring but intelligent capturing targeted at specific goals.”
Modules such as “Device Fingerprint Analysis” and “Social Relationship Analysis” are also present in the interface, indicating the system’s capability to identify users based on device characteristics and behavior paths. These modules involve endpoint parameter comparison, account correlation path tracking, and integration of cross-platform behavior data, centralizing various data sources into one system.
Wei Mian, an internet professional in Shenyang (alias), expressed to reporters that upon seeing the analysis modules related to device fingerprints and social relationships, he is more concerned about the technical direction behind them. He stated, “The emphasis isn’t solely on this image itself but on the direction it reflects. Over the years, we can see that related technologies are shifting from content processing towards individual identification.”
In recent years, the CCP has been intensifying its control over the cyberspace. Zhang Liang, a scholar from Beijing (alias), told reporters, “If a system like this exists, its focus has shifted from content management to identity targeting. It used to be about what you say; now it’s about affirming who you are, where you are, and who you are connected with. Once identities are structured, subsequent control no longer relies on single pieces of information but unfolds towards the entire person.”
He added, “From the interface, the inclusion of family members, devices, and social relationships within the same platform indicates its ‘relationship extension’ capability, meaning it can extend from one account to real-life social networks. If used for law enforcement or stability maintenance, this approach will alter existing management methods.”
Zhang pointed out that such platforms embody the continuous strengthening surveillance logic under the CCP regime. By targeting individuals through data modeling and extending to real relationships, this signifies a deepening control over individuals, further compressing people’s expressive space in both reality and cyberspace.